In August (yes, it took me this long to blog about it), Chris and I attended two “hacker” conferences in balmy Las Vegas (I don’t know who decided these things should be in the desert in August…), Black Hat and Defcon. I wanted to introduce Chris to the dark side of his industry, and he was able to convince his employer that, as a firmware designer, it would be good to go to Cybersecurity conferences. As it turns out, they ended up being glad he went (more about that later).
What are these conferences? I’ve been to Defcon twice now, once with Chris, and once with my friend, June, and I think this writer at Null-byte sums it up pretty well: “The con is the combination of some of the most brilliant minds in the industry, some of the most annoying pranksters, and a few well-meaning drunks.” (I’m not sure if Chris, June, and I quite fit any of those categories.)

Both conferences are attended by people from all around the world, but primarily, of course, from the US. For example, during Defcon, I had lunch with a member of the German secret police. Neither of us talked about our work, and we focused on the quality of pizza in Vegas. Black Hat is more of a professional conference, with lots of relevant (read that “terrifying”) information about the current state of cybersecurity. Defcon could be characterized as the carnival (and 90% less expensive) version of Black Hat. Are there real hackers there? For sure. Are there also a ton of FBI, CIA, and other three-letter agencies? Absolutely. As a matter of fact, one of the unofficial games at Defcon is “Spot the Fed”.
I will focus primarily on what we learned at Black Hat, because Defcon presentations were very similar, with the exception of the Villages, which were hands-on opportunities to see everything from voting machines to medical devices hacked, and learn to pick locks. Chris attended sessions on things I didn’t understand, like low-power Bluetooth. I attended more general (“interesting”) sessions.
So Chris did attend that session on low-power Bluetooth, because he has helped develop a low-power Bluetooth chip, which is currently being implemented in a wearable glucose-monitoring device. Coming out of the session, he told me the hack was “impressive work for a novice”. On Monday, as soon as we got back to work, the Nerd News was abuzz with this hack, and his company’s customers and his management were having a not-so-minor freakout. He was able to tell them that he was in that seminar, he understood the hack, and he had already implemented the security protections on their chip before the hack ever became public. So, the company immediately saw the value of sending him to the conference.
The most interesting sessions I attended were on attacks of Industrial Control Systems (ICS), satellite communications (SatCom), and implanted medical devices (follow the blue links for articles about each of these topics). Industrial Control Systems control factories, but more importantly, they control our utility infrastructure. They are notoriously vulnerable to attacks, and have been a huge concern to me since before I got into Cybersecurity. The SatCom vulnerability allowed the researcher to “see” and track every plane in the sky using their WiFi systems, but thankfully did not allow direct access to the planes’ control systems. Although there is apparently a theory (not well substantiated) that Malaysian flight 370 was hacked. Of even more concern to me, he was able to use this vulnerability to pinpoint every military base we have (including Top Secret bases) that uses SatCom (that would be all of them). He didn’t leave that slide up very long, because he had notified the military, and they were correcting the problem.
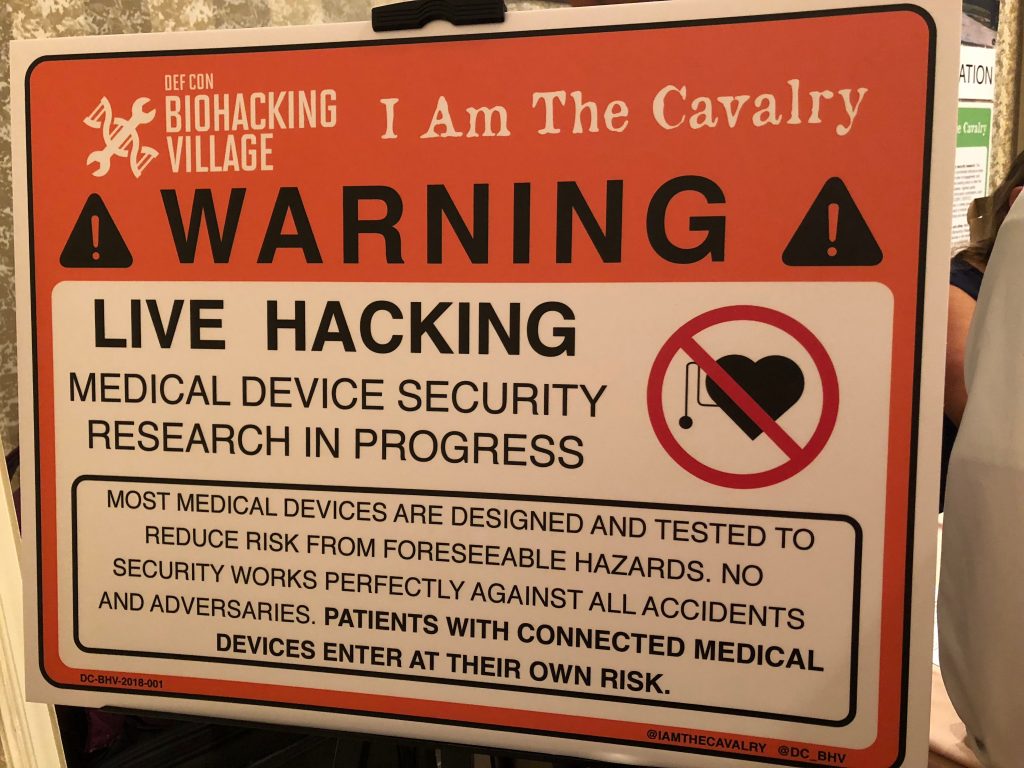
Of great concern to us personally was the hacking of implanted medical devices, since Moriah had a neurostimulator surgically implanted in May for her pancreatic pain. The session focused on more deadly devices like pacemakers and insulin pumps, but I asked a question at the end of the session about neurostimulators, and because of that, I met Suzanne Schwartz, who is the head of the FDA’s Medical Devices Division. Because of our vested interest in medical devices and my cybersecurity knowledge, Suzanne asked me to sit on two panels at an FDA workshop in Washington, DC, next week on Medical Device Cybersecurity. I was delighted that Chris had enough reward miles saved up to come with me. I will update you on that when we return home. I also met the head of I am The Calvary, a white hat (the good guys) hacking organization that hacks biomedical devices to find and report vulnerabilities to manufacturers. He leads the Biohacking Village at Defcon. We spoke a couple weeks ago, and he was asking how they could help the technical people hacking the devices feel more empathy for patients with devices, and I introduced him to Moriah’s art. He now wants to feature her art at this year’s Biohacking Village. And those folks are serious about what they’re doing (I could say “as serious as a heart attack”, but that might be a bit too accurate). The following sign was up at the Village when we visited (Moriah is not welcome there).
If you’re interested in reading all the news coming out of Black Hat, check out this link. There was way too much to summarize here, and there may be things you’re interested in that I didn’t cover (like hacking cars and voting machines, for example).

Recent Comments